Thanks @gordon451, sounds like a plan!
Not a bad idea, but I’d go a bit further: how about logging up to a given size, say 50KB, then close and archive while starting a new file. Date/time-stamping the archive files would also be useful. I’ve often pondered the concept of automatically deleting older archives–say 6 or 12 months–but OTOH the moment you delete the file you find you need it! I think this must be up to the user really.
A manual method could be enabled: if the log file does not exist, the app builds a new one, so you can simply pull the old one (with GW stopped!!!) into an archive folder. Could GW survive tooth extraction without anaesthetic?
I really want to see custom color. open a color selector for DL/UL and use those colors.
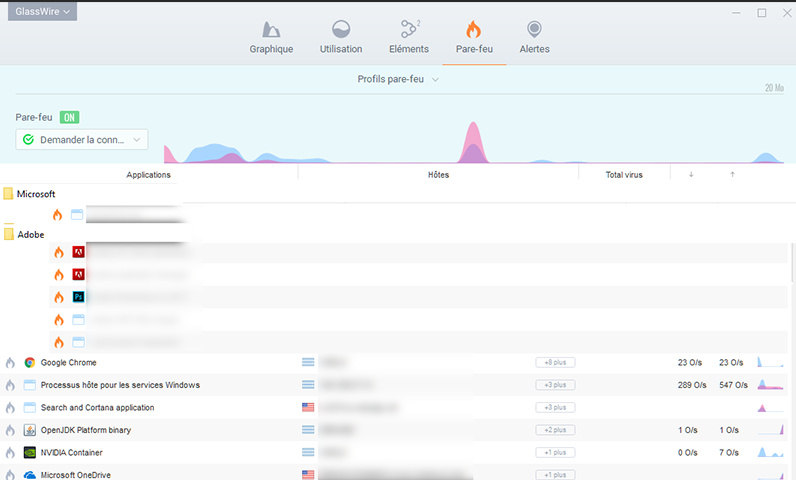
I’would like to manage directory in firewall tab to put application by family class.
For example a directory Adobe, Microsoft, etc.
By this way it’s more easy to find application in this tab.
Ohh and thanks for your soft. I really like it!
I took the Basic to encourage you and have some features.
I’ve downloaded the software before and I was really impressed with some of the features of it, however I also completely agree with your points so far.
I don’t think that it’s really a firewall at present. What I see it as, is a kind of process explorer for networks with a few nice touches around it; for instance the integration with Virus Total is a really good idea and it visualises traffic pretty nicely - although I admit that this could be better.
So far my suggested areas of improvement are:
-
If you’re going to create, advertise, and sell a firewall feature, it would be great to create a firewall feature that allows proper configuration. I’m not going to repeat it, but I pretty much echo the comments of @PhilipGoddard.
-
A free/open source management console. I am using your product on my home Windows estate and find that it’s really useful/interesting at investigating bandwidth hogs, beaconing, and processes that are acting nefariously or insecurely. In order to do this, I have to log onto each device individually and manually check what’s going on. What would be really useful, especially as you progress as a company, would be a centralised web-based management, monitoring, and logging console. If you are to break into the corporate arena which, lets face it, is where the money is, this needs to be created ASAP.
-
Which brings me onto: A logging solution that is either stored plain-text or can be exported via syslog. I can see a real-world use for this product in many security environments. One of the benefits of it is that it gives a lot of information without blocking traffic; which is absolutely crucial to availability-critical applications. If this information could be put into a syslog format and formatted, or stored in an external flat-text file for collection by an agent, this data could be harvested directly into a SIEM and used to aggregate against other log files and help analysts create a much better picture. It may do this already, but I haven’t been able to find it. If it can, could someone kindly point me in the direction?
-
More difficult and probably too much of a step towards a HIDS solution, but implementation of “smart” rule sets. What would be really great is if the product could use the data that it presents and look for potential nefarious patterns. For instance, a Word/Excell document starting a Powershell script, or numerous packets of the same transport-layer protocol coming from the same source to different ports without establishing a session could be an indication of a port scan. If you could somehow create these alerts, AND push them into some form of centralised logging capability, this could be a really powerful tool for both the security community and enterprise alike.
one thing unless it was already mentioned would be a way to allow/deny this now for a short while but keep it away from the list (or delete later) and if needed ask again, especially with setups it’s annoying to have a metric f-ton of entries of setups or whatever genericly named applications that wanted internet, because they are on the list no matter whether accepted or denied.
would very much like to see GlassWire implement something like the network monitor with world map in Little Snitch on OSX

Please remove the Inactivate Apps area as i find it a total waste.
Firewall tab request: Move the ‘Delete App’ function (small ‘x’) in the center of the firewall list into the ‘Info’ popup for the application icon, and group with the ‘Virus Scan’ and ‘Hide App’ buttons’.
I just found this today. Well hidden in an odd place as it is now…
Firewall tab request: Add sort, quick filter, and/or search to this list. This has been mentioned along with other requests, but I thought it also deserved a specific mention for this tab.
Being able to set the maximum period which the history is kept would be nice.
I’d like to see in the “Things” display, the amount of traffic currently going through each device/MAC address. I’d like this so in periods of super-slow wireless response I might identify the culprit.
The firewall can see IP addresses, why can’t we click block that IP address if we want to? Maybe a connection has some rouge IP connecting for no reason, we should be able to put a block on it but yet let the main program still connect.
To the GlassWire Team
Really hoping to see this feature I had mentioned in other threads. It’s is a pain! having to always turn ON turn OFF “Incognito” mode all the time, depending on what web work i am doing.
It would be wonderful to have the capability to exclude an application from the Usage tab and Host list. An example would be to exclude browsers of choice.
I know one can select “Incognito” but that stops everything from showing up while it’s on.
There could be an option in GlassWire to browse for the application .exe and exclude it in a list?
Perhaps another way, and could be easier to implement. Under Usage-Apps when you “Hide App” it stops and does not record “ANY” info/data at all. No Host traffic, no websites you visit etc… Having all the websites one might visit listed under the Usage-Host, can be a real privacy issue.
Thanks again.
You are not the only person to request this. Instead of detecting browsers, perhaps we can just offer the option to completely ignore certain applications completely as you suggest.
Thank you Ken for the reply.
Yes which ever is the easy way for the Dev-team to implement this, would be my no1 request.
Thanks again
hat would be hard, because we have switches, not hubs meaning everyone can only see his own transactions.
@Ken_GlassWire
One Feature I would Request would be (basically 2 sides of the same coin)
- Allow for a while, then forget (at least in the firewall)
- deny and forget later
especially since you cannot just close the permission request, software that only gets executed once and never again will clutter up the list of the direwall (e.g. some updaters which sometimes are stored with version numbers meaning each version is guaranteed to be a new file)
and it kinda gets annoying having a way too long list of totally unneeded stuff.
Hi all - the holiday season is brutal 
Anyway, @Ken_GlassWire, how are we travelling with multi-user profiles? I did look at Profiles in the latest version (2.0.91), but the info there is limited and doesn’t look like user profiles where I can hide the interface from users.