What are some distinct patterns or bits of information that Glasswire can display that might suggest you have spyware on your computer or have been hacked?
For example, what would it look like if someone was monitoring what you were doing? Would there be a steady stream of uploading? Would the upload be greater than the download stream for simple text browsing sites? How much data would this appear as? What’s the minimum upload rate that could appear if someone was spying on you (for example, just keylogging vs actual video screenshots, etc.)
I haven’t noticed heavy upload patterns, but I’m sure some spyware wouldn’t work this way. I’m looking for any possible tips or general advice that you may offer to watch out for.
@Window
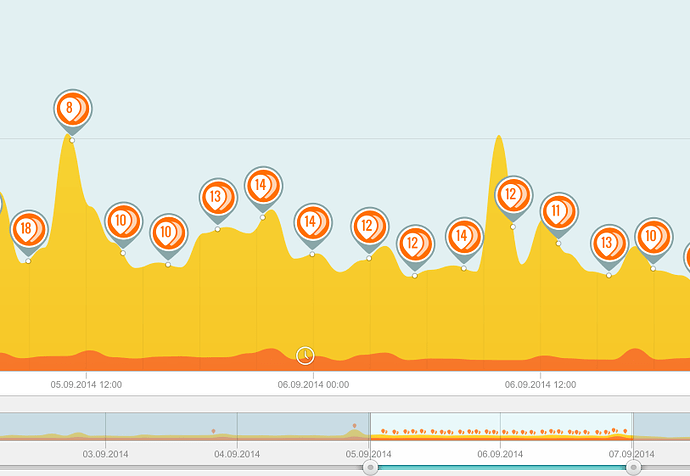
One of our first users found malware his antivirus missed and we blogged about it here https://blog.glasswire.com/2016/12/19/detecting-malware-with-glasswire/. In his case his computer was connecting to multiple proxies and sending out lots of data at night while his PC was idle. His graph looked something like this:
You can see from the screenshot that during the time period all of this was happening the graph is shaded and it shows a clock icon, so all this strange activity happened on an idle PC over a long time period.
The theory behind GlassWire is that any kind of malware or privacy violating application will probably have to make some network related change to your PC, and hopefully GlassWire will help you catch it. For example every time a new application accesses the network GlassWire warns you with a “new” alert.
GlassWire can also tell you when your DNS server is changed, if something changes your host file, or if an application connected to the network changes its hash, version, or loses its cert, or has a cert change. You may notice this when Chrome or Firefox auto-update. GlassWire will tell you that Chrome/Firefox has changed in those cases.
The paid version of GlassWire can tell you if a new unknown device joins your WiFi network.
If you think you may have malware here is a guide that can help. https://www.glasswire.com/malware/
Unfortunately all malware is different so there is no exact specific alert GlassWire gives like an antivirus, but instead you have to read GlassWire’s data yourself and make an informed decision from that data.
Ok, so the following are some ways that that it can help detect malware:
- Connecting to multiple proxies
- Identifying new applications
- DNS server changes
So the primary way of detecting malware is by observing the notifications for anything suspicious? Is there any other ways that other users have used this tool to identify questionable applications/activity?
@Window
Here are some more ways to identify questionable apps/activity.
-
Go to the GlassWire Graph or Usage tabs and check the traffic types listed. Does something look unusual there? Click the icon to see what apps were involved. We use an API to detect traffic types and it’s not perfect but it’s pretty close.
-
If you click an app under the “Firewall” tab and click its icon you can choose “Virus Scan”. We use the Windows Defender API from Windows.
-
Check the country flag for any network activity. If you think it’s unusual for your PC to be communicating with a server in an unusual country from an unusual application then it could signal something is wrong. However lots of companies use content delivery networks now and I have noticed Microsoft sometimes can communicate with Chinese servers for example. My Office subscription contacted their Hong Kong server yesterday even though I’m in the USA. GlassWire also does an nslookup on your connections so you can see the host name most of the time.
-
Check your local vs external traffic. Go to GlassWire’s usage tab and look above the left side “All Usage” option, then to the right there is an “Options” with a pull-down menu. If there is unusual activity on your local network it could identify malware trying to move laterally across your network to another device you own.
-
Since GlassWire collects historical data you can look at your Usage stats over a long period of time to pick out strange activity.
-
Recently I was getting a lot of ARP spoofing alerts from GlassWire. I figured out a device on my network was configured incorrectly and it kept trading IP addresses with another device and allowed me to fix my network so it worked properly. For me this was not a security concern, but for others it could be.
-
GlassWire uses some third party sources to keep a list of suspicious hosts and updates it daily. If you connect to a known suspicious host GlassWire will warn you. This is why GlassWire itself accesses the network once per day (to check for updates and to update suspicious hosts). https://www.glasswire.com/privacy/ If you don’t like this you can make GlassWire block itself and of course GlassWire shows its own network activity on its own graph. Our Android app has no ability to access the network at all.
During development we were inspired by Richard Bejtlich’s network security books. His books are usually about monitoring the entire network, but we got some ideas on things to monitor to help with security when designing GlassWire. People like Bejtlich can often find threats and malware on networks by only using open source tools like Snort or Bro. We wanted to allow normal people who are not extremely technical to have the ability to hunt for unusual activity on their own PCs and we hope GlassWire helps people do this.
We have also learned there is an entire audience of people out there who have very limited Internet connections in rural areas and they use GlassWire in non-security ways. For example they may go to GlassWire’s settings and turn on our “bandwidth overage monitor” to get alerted before they go over their ISP limit for their PC. Our Android app is currently mostly about data usage in this way to help people stay under their data limits but more security and privacy features are on the way.
Privacy is also a big thing for many GlassWire users. Some apps may not necessarily be malware but if they are phoning home GlassWire will tell you right away.
I hope this helps!
1 Like