I made a whoopsy-daisy when I installed GlassWire and activated it’s firewall, the firewall I used before this was open source software that used Windows Filtering Platform and bypassed the Defender firewall completely, but the Defender firewall relentlessly didn’t shut up about not being on.
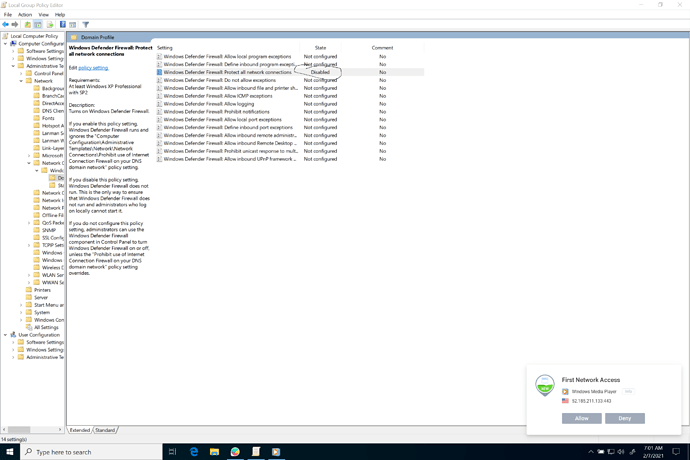
So I disabled it through the group policy:
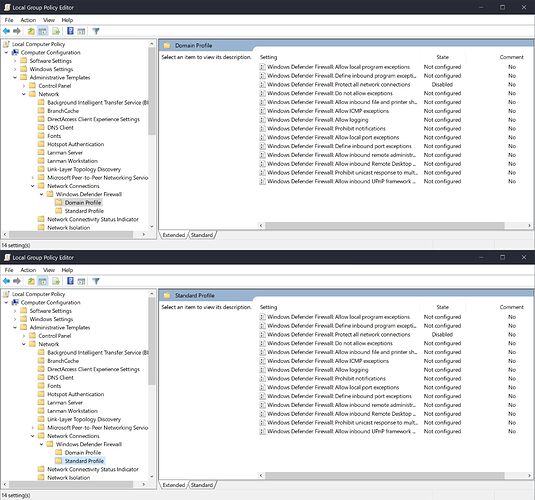
Computer Configuration > Administrative Templates > Network > Network Connections > Windows Defender Firewall > Domain Profile > Windows Defender Firewall: Protect all network connections
and
Computer Configuration > Administrative Templates > Network > Network Connections > Windows Defeder Firewall > Standard Profile > Windows Defender Firewall: Protect all network connections
But as you can guess, they where still disabled when I activated the GlassWire firewall.
GlassWire was completely ineffective and happily wasn’t blocking anything without showing any sign that the buttons where just for show, until I remembered what happened and reversed the policy.
I don’t think this happens every day but an effectiveness test could be useful in some cases.
@WearingThePurple
Sorry for the problem and thanks for your feedback. We will look at group policy settings and see if we can recreate this.
We use the Windows Firewall API for blocking because it uses almost no resources, it is compatible with other Windows software, it’s stable, and we have found it to be reliable. Over a billion Windows users have this API so it’s tested and heavily used. The other nice thing about this API is that even if GlassWire is not running its blocking will still be in place, for example when booting up or shutting down.
@WearingThePurple
May I ask your OS version? I tried this on a VM and I could not recreate the issue.
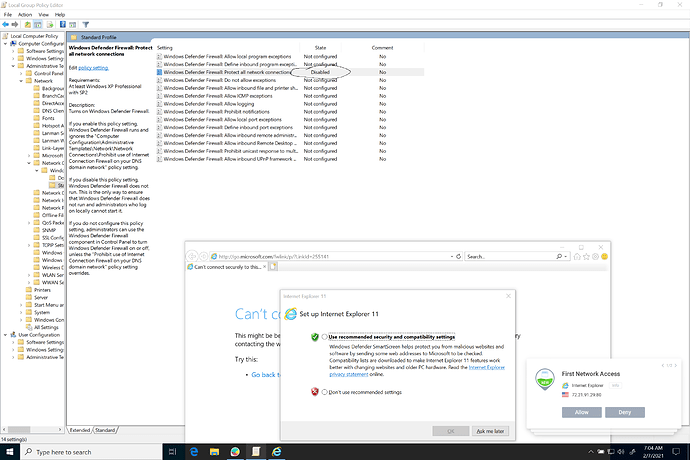
I disabled the two group policy options while in GlassWire’s “Ask to connect”. I launched Windows Media Player and IE (both apps that I know try to access the network) and I received a prompt for both and they seemed to be blocked. I was using Windows 10. Did you have our free or paid app?
You can see the screenshots below. If you got different results please let me know if I missed something and I’ll test again. Maybe I did something wrong?
Thanks for your report. I was using GlassWire Pro 2.2.291 on Windows 10. Perhaps these particular group policies make no changes to the APIs we use.
1 Like
Sure thing, I’m using Windows 10 Enterprise 20H2 (19042.789), with GlassWire Basic 2.2.291.
I’ll go back and try to recreate the issue for myself here, I’ll get back with you with the results.
I’ve always loved that feature in a firewall.
@WearingThePurple
I agree with you that we should put up a notice of some type if our firewall is somehow disabled. I believe we do this already if a third party antivirus disables it, and then we actually even show the name of the app causing it.
One easy way to check the issue you reported with group policy is to be sure you’re in “ask to connect”, then launch an app that accesses the network and see if you get a prompt or not. Unless this causes some issue that makes the test not correct? Let me know what you find.
I was using the Windows sandbox.
I successfully recreated the issue.
1. I set the policies preciously mentioned to disabled.
2. I set Firefox, who was previously unblocked, to blocked.
3. Went online, cleared my cache, force reloaded several websites & clicked on links I haven’t previously visited.
Every website was accessible at this point and GlassWire mentioned a first connection of a background application that has always been blocked.
4. I set the policies previously mentioned to not configured.
5. Went online & force reloaded a couple websites.
Every website was blocked at this point
You’re right it didn’t, that does help.
2 Likes
@WearingThePurple
Thanks, I will share this with our team and try to recreate it again. I’m sure you confirmed our firewall was set to “on”, correct?
It was, the change of the policies was enough to block Firefox.
1 Like