There is a 0-day vulnerability in Windows that is caused by the Windows Print Spooler.
You should disable the Windows Print Spooler until the issue is fixed.
There is a 0-day vulnerability in Windows that is caused by the Windows Print Spooler.
You should disable the Windows Print Spooler until the issue is fixed.
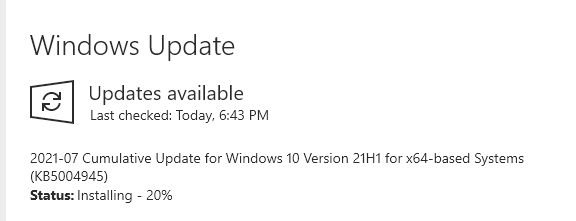
A patch is now available. Please run Windows Update!
Title: Microsoft Security Update Revisions
Issued: July 6, 2021
Summary
=======
The following CVE has undergone a major revision increment.
======================================================================================
CVE-2021-34527 | Windows Print Spooler Remote Code Execution Vulnerability
Version: 2.0
Reason for Revision: CVE updated to announce that Microsoft is releasing an update
for several versions of Window to address this vulnerability. Updates are not yet
available for Windows 10 version 1607, Windows Server 2016, or Windows Server 2012.
Security updates for these versions of Windows will be released soon. Other
information has been updated as well. This information will be updated when more
information or updates are available.
Originally posted: July 1, 2021
Updated: July 6, 2021
Aggregate CVE Severity Rating: Critical
Other Information
=================
Recognize and avoid fraudulent email to Microsoft customers:
=============================================================
If you receive an email message that claims to be distributing a Microsoft security update, it is a hoax that may contain malware or pointers to malicious websites. Microsoft does not distribute security updates via email.
Get it via Windows Update!
Thank you for these extra details @TripleHelix!
My take on this vulnerability is that it’s only a concern for Windows domain controllers (servers). So mostly an enterprise network issue for the print spooler.
So if you are a Windows home user that is NOT attached to a Windows domain, there is probably nothing to worry about this time. The advisory did not specifically mention this, but they probably should have.
In any case, it doesn’t hurt to stay patched and up to date!
The PrintNightmare bug tracked as CVE-2021-34527 enables attackers to take over affected servers via remote code execution (RCE) with SYSTEM privileges.
Thanks @zzz00m.
I’m glad the problem is less likely to be an issue for home users.
Yep, me too! I always like to drill down on the scary vulnerability headlines to see what is truly affected, before I panic. 
There are publications out there that often use click-baity headlines to get user eyeballs… and then some of the articles are sometimes so techy that it would take an expert to parse the “does this affect me” truth.
FYI, this issue still keeps on going…
You can also find fixes for the PrintNightmare vulnerability within Windows itself by following these steps:
Hope This Works,
Peter