Firewall tab request: Add sort, quick filter, and/or search to this list. This has been mentioned along with other requests, but I thought it also deserved a specific mention for this tab.
Being able to set the maximum period which the history is kept would be nice.
I’d like to see in the “Things” display, the amount of traffic currently going through each device/MAC address. I’d like this so in periods of super-slow wireless response I might identify the culprit.
The firewall can see IP addresses, why can’t we click block that IP address if we want to? Maybe a connection has some rouge IP connecting for no reason, we should be able to put a block on it but yet let the main program still connect.
To the GlassWire Team
Really hoping to see this feature I had mentioned in other threads. It’s is a pain! having to always turn ON turn OFF “Incognito” mode all the time, depending on what web work i am doing.
It would be wonderful to have the capability to exclude an application from the Usage tab and Host list. An example would be to exclude browsers of choice.
I know one can select “Incognito” but that stops everything from showing up while it’s on.
There could be an option in GlassWire to browse for the application .exe and exclude it in a list?
Perhaps another way, and could be easier to implement. Under Usage-Apps when you “Hide App” it stops and does not record “ANY” info/data at all. No Host traffic, no websites you visit etc… Having all the websites one might visit listed under the Usage-Host, can be a real privacy issue.
Thanks again.
You are not the only person to request this. Instead of detecting browsers, perhaps we can just offer the option to completely ignore certain applications completely as you suggest.
Thank you Ken for the reply.
Yes which ever is the easy way for the Dev-team to implement this, would be my no1 request.
Thanks again
hat would be hard, because we have switches, not hubs meaning everyone can only see his own transactions.
@Ken_GlassWire
One Feature I would Request would be (basically 2 sides of the same coin)
- Allow for a while, then forget (at least in the firewall)
- deny and forget later
especially since you cannot just close the permission request, software that only gets executed once and never again will clutter up the list of the direwall (e.g. some updaters which sometimes are stored with version numbers meaning each version is guaranteed to be a new file)
and it kinda gets annoying having a way too long list of totally unneeded stuff.
I agree. We are working on this and it’s a very common request also, thanks!
Hi all - the holiday season is brutal 
Anyway, @Ken_GlassWire, how are we travelling with multi-user profiles? I did look at Profiles in the latest version (2.0.91), but the info there is limited and doesn’t look like user profiles where I can hide the interface from users.
I totally agree with your idea about blocked items. I too have to scroll down to see what is active. The blocked tab would be a great idea.
I’d really like the ability to add custom notes to Firewall items.
For example, an app I don’t recognise appears in my usage feed such as ‘Microsoft Feeds Synchronisation’. I have no idea what this is, so I head of Google to try and research it and find out what it is. Eventually I figure out it’s something I don’t need and don’t want it to use any of my bandwidth, so I block it.
As time passes, similar events occur and I block other services.
Fast forward 6 months, something I try to do on my PC doesn’t work and it appears to be because of a Firewall restriction I’ve added. If I had notes on each item I’d blocked about what they were and why I’d blocked them, it might help me work out which item it is that I need to unblock, since realistically I’m not going to remember the purpose of every app process I’ve ever blocked.
It may not add huge benefits but then it doesn’t seem like it would be all that hard to implement either, and would be very useful under the circumstances I just described.
I’m also looking for a firewall mode that blocks generally everything and as soon as an application tries to connect for the first time you show a popup with the question if the program should be blocked or allowed and if this choice shall be remembered or not. Also make it possible to add programs manually to the list to be able to block them or not. I mean this fw section doesn’t even deserve the name firewall. what if you want to block a program from the beginning and not just after it already has sent out data? I had to leave comodo firewall as it’s incompatible with some apps I really need to use and comodo is just the best in terms of control etc. But Glasswire is not really a firewall imho. Sad because I like the app. it’s very clean, neat and seems to be running very smoothly.
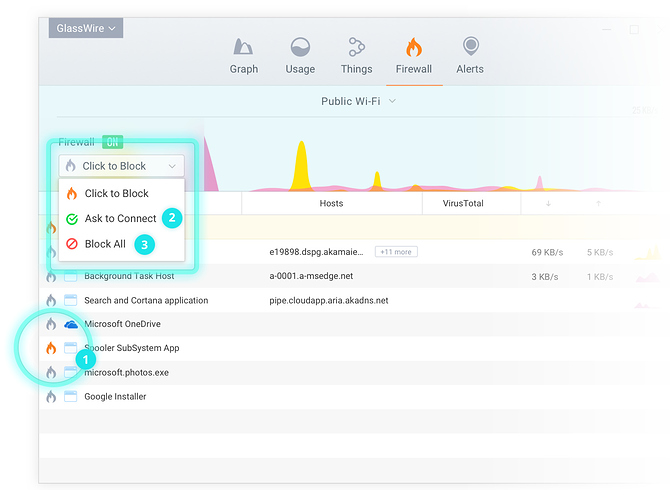
Go to “Ask to connect” mode to stop/allow new connections just as you describe.
https://www.glasswire.com/quickstartguide/
Very nice, this was going to be my next request. Spot on 
‘Ask to connect’ = default deny. So this feature is working for me as expected. I can keep all of the ‘chatty’ apps on the leash with this. If I happen to step away when something tries to connect for the first time … denied!!!
It is always good to review your list of apps in the firewall, for apps that you may have blocked inadvertently, and vice versa. If not sure, you can delete any line item so that you will be prompted again the next time a connect is attempted for that item.
the one annoying this is that you cannot add a program to the list (no matter whether black or white) before it does anything which can get REALLY annoying, ESPECIALLY with setups that unpack themself to a random folder in temp try to get online and dont have a retry button, basically forcing you to set it to click to block, but that means that OTHER software can get through without asking as well.
It’s been mentioned a number of times before, but definitely enhancing the “Ask to Connect” to include a feature set similar to LittleSnitch on OS X would be great – even if it’s an “advanced” setting disabled by default:
- Permanent/Temporary option, with “Until Quit/Logout/Restart” and “Time-based (ie, 5 minutes)” temporary options
- Ability to specify granular rules on the host. In other words, block only a specific host/wildcard/ip for an application instead of all-or-nothing. For example, give general access to an application, but block access to “example dot com”
LittleSnitch also provides ability to specify port and protocol (TCP/UDP) limitations but I find that the domain/ip is enough for my purposes.
Hi Ken
Any news on this feature. I still have to leave “Incognito” on permanently, until this new feature would be added to GW Thank you.
This is on our “todo” in the near future list.